Nexus Market Links
Verified Nexus onion URLs, darknet mirrors & official .onion addresses
Find every official Nexus Market link in one place — PGP-signed onion URLs, backup darknet mirrors, and cryptographically verified .onion domain addresses. Only use these authentic Nexus marketplace links to safely access the real market.
Official Nexus Market Links
Every Nexus Market URL listed below is a verified tor hidden service link. Always verify the authenticity of each Nexus onion mirror using our PGP signature before entering credentials. Learn more about security measures and browse our marketplace.
Security Warning
Always verify links using our PGP signature. Beware of phishing attempts and fake mirrors. Nexus administrators will never ask for your password or private keys.
Verify PGP Signature
mQINBGJhX3YBEAC7t7PpHL+Vz0XGRlHgUNQnWbQNQCU2xtpSX/+7GyYTpEXnTxZV
KWzN8CsXg7R5RZ9Dj4vAu0eABu5Wl5Zp4U5qVJXm3VYFrRKbA1ihYnVr0NEJqXrj
NcBtJZA7Km+S8zZ2M9981HQZ5ZkAVtXi/8TmYV7/cHQvOdQIeOdgWGJxvtYYkDFJ
... [PGP KEY TRUNCATED] ...
=X4Tz
-----END PGP PUBLIC KEY BLOCK-----
Security Guidelines
Follow these guidelines to ensure your safety when using any Nexus Market link or darknet mirror URL. Protect yourself from phishing and fake .onion addresses across the dark web.
What NOT to Do
- Never use regular browsers (Chrome, Firefox, Safari)
- Don't trust links from unknown sources
- Never share your credentials with anyone
- Avoid using public Wi-Fi networks
- Don't disable JavaScript security settings
Best Practices
- Always use the anonymous Tor browser with latest updates
- Verify PGP signatures before accessing
- Enable 2FA for additional security
- Use a dedicated device for dark web and darknet access
- Keep your operating system updated
Access Methods
Choose the most secure method for accessing Nexus Market links and dark web mirrors based on your security needs and threat model.
Basic Security
For casual users
- • Privacy browser (Tor)
- • Disable JavaScript
- • Use official Nexus Market links only
- • Enable 2FA
Enhanced Security
Recommended for most users
- • Tails OS or Whonix
- • VPN + Tor
- • PGP verification
- • Dedicated device
Maximum Security
For high-risk users
- • Air-gapped system
- • Multiple VPN layers
- • Hardware security keys
- • Physical isolation
System Status
Real-time monitoring of Nexus Market link infrastructure and darknet services.
Complete Tor Setup Guide for Nexus Access
A detailed, step-by-step guide to installing, configuring, and using the Tor Browser to securely access Nexus Market onion links and darknet mirror URLs. Updated for 2026 with the latest security recommendations for safe .onion domain access.
Download Tor Browser from the Official Source
Visit torproject.org and download the Tor Browser for your operating system. Tor Browser is available for Windows, macOS, Linux, and Android. Never download Tor from third-party websites, app stores, or links shared in forums — these may contain malware or modified versions that compromise your anonymity.
Verify the download using the PGP signature provided on the Tor Project website to ensure the installer hasn't been tampered with during transit.
Install and Launch
Run the installer and follow the on-screen prompts. On Windows, you can
install Tor Browser to a USB drive for portable, traceless usage. On Linux,
extract the archive and run ./start-tor-browser.desktop.
On first launch, click "Connect" to establish a Tor circuit. If you are in a
country that blocks Tor, select "Configure" to set up bridges
(see bridge
configuration section below).
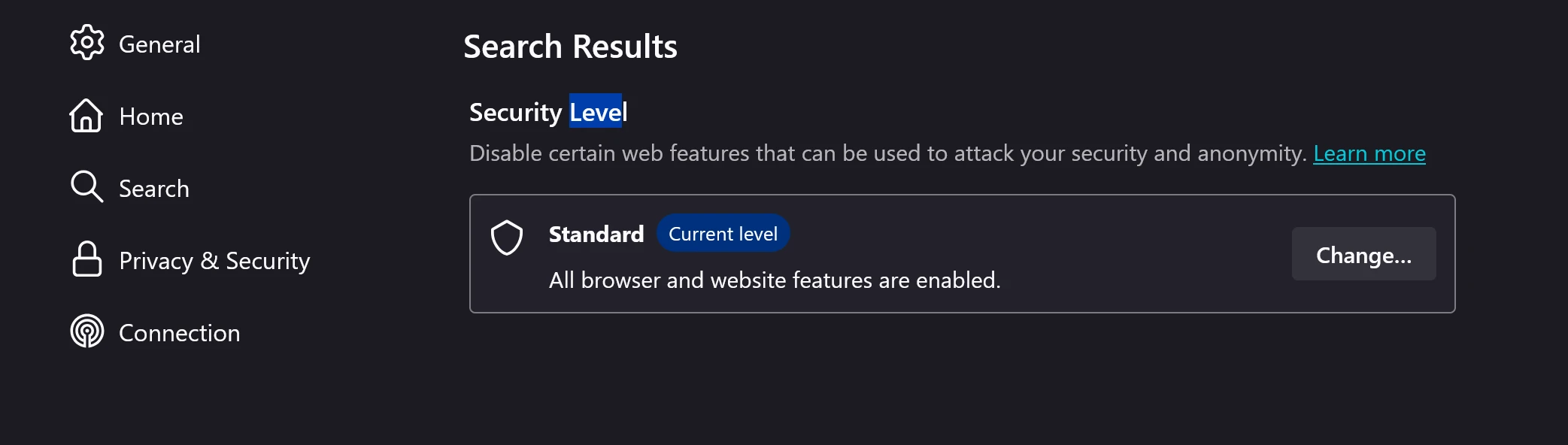
Configure Security Settings to "Safest"
Click the shield icon in the toolbar and select "Safest" security level. This disables JavaScript, blocks web fonts, disables media autoplay, and limits browser features that could be used for fingerprinting or de-anonymization attacks.
While the "Safest" setting may break some regular websites, it is strongly recommended for all Nexus onion link access as the marketplace is designed to function without JavaScript.
Navigate to a Verified Nexus Onion Link
Copy one of the official Nexus onion URLs listed at the top of this page and paste it into the Tor Browser address bar. Always type or paste the URL manually — never click links from untrusted sources. After the page loads, verify you see the official Nexus Market login page with the correct branding and security elements before entering any credentials.

Platform-Specific Recommendations
Windows
- • Install to a USB drive for portable use
- • Disable Windows Defender real-time scanning for Tor directory
- • Use a VPN before launching Tor for an extra layer
- • Clear the download folder after installation
macOS
- • Move Tor Browser.app to Applications folder
- • Allow the app in System Preferences → Security
- • Disable macOS Gatekeeper notifications
- • Use Little Snitch to monitor outgoing connections
Linux
- • Verify GPG signature of the download archive
- • Run from an encrypted partition
- • Consider AppArmor/SELinux profiles for isolation
- • Use Firejail sandbox for additional hardening
Tails / Whonix
- • Tails: Boot from USB, all traffic routes through Tor
- • Whonix: Run in VM with Tor gateway isolation
- • No traces left on host system
- • Recommended for maximum operational security
How to Verify Nexus PGP Signatures — Step-by-Step
PGP (Pretty Good Privacy) verification is the only reliable method to confirm that a Nexus onion link is authentic and has not been tampered with by phishing attackers. Learn how to verify in under 5 minutes.
What Is PGP and Why Does It Matter?
PGP (Pretty Good Privacy) is an encryption standard used to sign and verify messages, ensuring they come from a trusted source. When the Nexus team publishes official onion links, they sign each message with their private PGP key. By verifying the signature using their public key (published on this page), you can mathematically confirm that:
- The message was created by the Nexus team (not an impersonator)
- The onion URLs have not been modified since signing
- The message is not a replay of an old, potentially compromised link list
Step-by-Step Verification Process
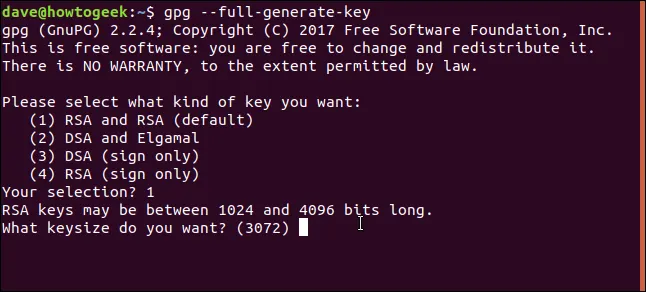
Step 1: Install GPG Software
Install GnuPG (GPG) on your system. It comes pre-installed on Tails and most Linux distributions. For Windows, install Gpg4win; for macOS, install GPG Suite.
sudo apt install gnupg
# macOS (Homebrew)
brew install gnupg
Step 2: Import the Nexus Public Key
Copy the Nexus PGP public key from the top of this page and save it to a file
(e.g., nexus_pgp.asc). Then
import it into your GPG keyring:
# Verify the key was imported:
gpg --list-keys "Nexus"
Step 3: Save the Signed Message
When Nexus publishes new onion links, they are distributed as PGP-signed messages. Save the
full signed message (including the
-----BEGIN PGP SIGNED MESSAGE-----
and
-----END PGP SIGNATURE-----
lines) to a text file:
nano nexus_links_signed.txt
# Paste the full signed message and save
Step 4: Verify the Signature
Run the GPG verification command. If the signature is valid, you will see "Good signature" — confirming the links are authentic:
# Expected output:
gpg: Good signature from "Nexus Market <nexus@onion>"
If you see "BAD signature" in the output, the message has been tampered with. Do NOT use any links from that message. Always obtain the Nexus public key from this official page (nexus-market.nexus) and never from third-party sources, forums, or direct messages.
How to Identify Phishing & Fake Nexus Links
Phishing is the #1 security threat for dark web marketplace users. Learn how attackers create convincing fake Nexus Market links and Nexus URLs, and how to protect yourself from credential theft on the darknet.

Common Phishing Attack Patterns
Attackers use several techniques to create fake Nexus Market links and counterfeit Nexus URLs that appear identical to the real marketplace. Understanding these patterns is your first line of defense:
-
Typosquatting
Attackers register .onion addresses that are nearly identical to the real Nexus URL, changing just one or two characters. These are distributed via darknet forums, Dread posts, and paste sites. Always copy links from this official page — never from forum threads.
-
Homoglyph Attacks
Using characters from different alphabets that look identical to Latin letters (e.g., Cyrillic "а" vs. Latin "a"). In the context of .onion addresses, attackers generate addresses with similar-looking character sequences to trick users into thinking they're on the real site.
-
Fake Mirror Listings
Fraudulent "mirror list" websites that claim to provide updated Nexus Market URLs but instead redirect to phishing clones. These sites often rank in search engines and use SEO manipulation to appear legitimate. Only trust links from nexus-market.nexus.
-
Man-in-the-Middle Proxies
Some attackers run Tor exit nodes or create transparent proxies that intercept traffic to Nexus, injecting modified login pages to steal credentials. Using the official .onion address (which uses end-to-end encryption) instead of any clearnet proxy eliminates this risk entirely.
Quick Verification Checklist
Before entering any credentials on a Nexus login page, verify ALL of the following:
Understanding Nexus Mirror Infrastructure
Nexus maintains multiple .onion mirror URLs to ensure continuous availability even under heavy traffic loads or targeted denial-of-service attacks. Each Nexus Market mirror link is a verified darknet access point connecting to the same backend infrastructure.
What Are Onion Mirrors?
An onion mirror is an alternative .onion address that connects to the same Nexus Market backend infrastructure. All Nexus Market link mirrors share the same database, same user accounts, and same listings — the only difference is the entry point Nexus URL. Mirrors exist to provide redundancy and load balancing, ensuring that even if one dark web address is unreachable, users can still access the darknet marketplace through another.
Why Does Nexus Use Multiple Mirrors?
- DDoS Protection — Distributing traffic across multiple addresses mitigates distributed denial-of-service attacks that target a single URL
- Geographic Distribution — Mirrors are hosted across different Tor circuits, reducing latency for users in various regions
- Rotation Schedule — Nexus periodically rotates mirror addresses to stay ahead of censorship and blocking attempts
- Failure Resilience — If the primary link is taken down, mirrors ensure zero downtime for the marketplace
Primary vs. Mirror — Comparison
| Feature | Primary Link | Mirror Links |
|---|---|---|
| Database | Shared | Shared |
| User Accounts | Same | Same |
| Update Priority | First | Within Minutes |
| Uptime Guarantee | 99.9% | 99.5%+ |
| DDoS Target Risk | Higher | Lower |
| Recommended For | Default Use | Backup / Fallback |
Nexus rotates mirror addresses periodically for security reasons. Always check this page for the latest verified URLs. Bookmark nexus-market.nexus as your single source of truth for all official Nexus Market onion links.
Tor Bridge Configuration for Censored Regions
If you live in a country that blocks Tor traffic (China, Iran, Turkmenistan, Russia, Belarus, etc.), you can use Tor Bridges and pluggable transports to bypass censorship and access Nexus Market.
What Are Tor Bridges?
Tor Bridges are unlisted Tor relay nodes that act as entry points into the Tor network. Because they are not publicly listed, they cannot be easily blocked by government firewalls or ISP filters. When combined with pluggable transports, bridge traffic is disguised to look like regular HTTPS traffic, making it virtually undetectable.
Available Pluggable Transports
obfs4 (Recommended)
The most widely-used pluggable transport. Obfuscates Tor traffic to appear as random network noise, defeating deep packet inspection (DPI). Effective against most censorship regimes. Available built-in with Tor Browser.
Snowflake
Uses WebRTC to route Tor traffic through volunteer peer-to-peer proxies. Traffic appears as video conferencing data. Highly effective in China and Iran where other methods are blocked. No configuration needed — select "Snowflake" in Tor Browser settings.
meek-azure
Routes Tor traffic through Microsoft Azure CDN, making it appear as legitimate cloud service traffic. Effective but slower due to CDN overhead. Use as a last resort when obfs4 and Snowflake are blocked.

How to Configure Bridges
Option 1: Built-in Bridges (Easiest)
- 1. Open Tor Browser → Click "Configure"
- 2. Check "Tor is censored in my country"
- 3. Select a built-in bridge type (obfs4 recommended)
- 4. Click "Connect"
Option 2: Request Bridges via Email
- 1. Send an email to bridges@torproject.org
- 2. Include "get transport obfs4" in the body
- 3. Use a Gmail or Riseup email (required for anti-abuse)
- 4. Enter the received bridge lines in Tor Browser settings
Option 3: BridgeDB Website
- 1. Visit bridges.torproject.org
- 2. Select your preferred transport type
- 3. Solve the CAPTCHA to receive bridge addresses
- 4. Paste bridge lines into Tor Browser → Settings → Bridges
Nexus Links & Access FAQ
Frequently asked questions about accessing Nexus Market through the dark web, verifying Nexus Market links and Nexus URLs, and troubleshooting darknet connection issues.
What should I do if a Nexus mirror link is down?
If a Nexus mirror link is not loading, try the following steps: First, switch to a different mirror listed on this page — at least two mirrors are always online. Second, request a new Tor circuit by clicking Tor Browser → New Circuit for this Site. Third, check if your Tor Browser is up to date, as outdated versions may fail to connect. Finally, if all mirrors are unreachable, the marketplace may be undergoing scheduled maintenance — wait 30 minutes and try again. Always return to nexus-market.nexus for the latest verified links.
How often are Nexus onion links updated?
Nexus onion links are verified and updated on this page at least once every 24 hours. Mirror addresses are rotated periodically for security reasons — this rotation schedule is not publicly disclosed to prevent preemptive blocking. When a rotation occurs, the old mirror may remain active for up to 48 hours as a transition period before being decommissioned. Bookmark this page and check back regularly for the latest verified URLs.
Can I access Nexus without Tor Browser?
No — using Tor Browser is mandatory for accessing Nexus Market. The marketplace operates exclusively as a Tor hidden service (.onion), which is only reachable through the Tor network. Do not use so-called "Tor2Web" proxy services (like onion.ws or onion.to) as these are clearnet gateways that can see your real IP address and intercept your login credentials. Some of these proxies are known to be operated by malicious actors specifically for credential harvesting. Always download and use the official Tor Browser from torproject.org.
How do I report a fake Nexus phishing link?
If you encounter a suspected phishing link impersonating Nexus Market, report it through: 1) The Nexus Market support ticket system (accessible after login on the real marketplace), 2) The official Nexus channel on Dread (verify the admin PGP key), or 3) Post a warning in the relevant darknet forum with the fake URL clearly marked. Including a screenshot of the phishing page helps the team identify and warn other users more quickly. Never enter your credentials on a suspected phishing site — even for "testing" purposes.
Last updated:
Ready to Access Nexus?
Use our official Nexus Market links to access the most secure dark web marketplace. Always verify the Nexus URL authenticity and follow darknet security best practices.
